How cloud encryption can protect your data from cyberattacks and data breaches
How to set up face ID on your cellular device
Kurt "The Cyberguy" Knutsson teaches how to enable your ID on your cell phone.
Curious about the security of your documents in the cloud? You’re not alone. We recently received an email from Dana in Marietta, Ga., who is asking this,
"I just read your article on saving documents to the cloud. What is your opinion on protecting those documents by encrypting them first? Does that prevent companies like Google from harvesting them? Also, how are these files removed after the death of the individual?" - Dana, Marietta, GA
Wonderful question, Dana. Data encryption can be an overwhelming concept at first, but when broken down, it is simple.
Encryption is a process of transforming data into an unreadable form that can only be accessed by authorized parties with the decryption key, which is basically just a password that can turn the data back into text that can be read and used.
This makes it nearly impossible for anyone without access to steal, change, or compromise whatever you are protecting. You may choose to do this to protect sensitive files like financial or medical documents.
However, encryption does not guarantee complete privacy. Some companies, like Google, may have access to your encryption keys or use other methods to decrypt your data.
Therefore, encrypting your documents may not prevent Google from harvesting them, depending on how you use their services and what their policies are.
What are the benefits of cloud encryption?
The main appeal of cloud encryption is improved cybersecurity. Encrypting your documents before uploading them to the cloud can provide an extra layer of protection against unauthorized access, data breaches, hacks, malware and cyberattacks.
If or when data breaches occur on a site with your information, your data is much more likely to be safe if encrypted.
Should you encrypt your data before sending it to the cloud?
You can add an extra layer of security by encrypting your data yourself before sending it to the cloud. While most cloud services do encrypt your data automatically, they do so in a way that isn’t the safest or most private.
They can still read your data, and if a hacker manages to get into the server with your data, they can read it as well.
There are many really good third-party encryption apps that allow you to encrypt individual or large groups of files.
DON'T FALL FOR THIS NEW ROUND OF ICLOUD SUPPORT SCAM EMAILS
There are also built-in encrypting methods on both Windows and Mac. These methods can also help you password-protect certain important documents and files, like financial records or personal information.
How to encrypt on Windows
- Right-click on the folders you want to encrypt and go to properties
- Choose advanced under the general category
- Tick "Encrypt content to secure data"
- Click Ok and then Apply
- Select "apply changes to folder, sub folder, and files"
- Back up the file encryption key and store it safely
If you are encrypting only a single file and not a folder, it's just as easy.
- Right-click on the file you want to encrypt and go to properties
- Choose advanced under the general category
- Tick "Encrypt content to secure data"
GET SECURITY ALERTS WITH THE FREE CYBERGUY NEWSLETTER - CLICK HERE
- Click OK and then Apply
- Select "Encrypt the file and its selected folder
- Back up the file encryption key and store it safely
How to encrypt on Mac
This one is a bit more complicated and reserved for our more technically brave. If you are unsure about this process, you may want to try the following using dummy or test folders and files first.
- To begin with, please note that you can only encrypt folders which then protect the files within them.
- Create a folder on your desktop by right-clicking and selecting Create a new folder. Feel free to put any documents you may have in there.
- In the top left bar on your desktop, select Go, then scroll down and select Utilities
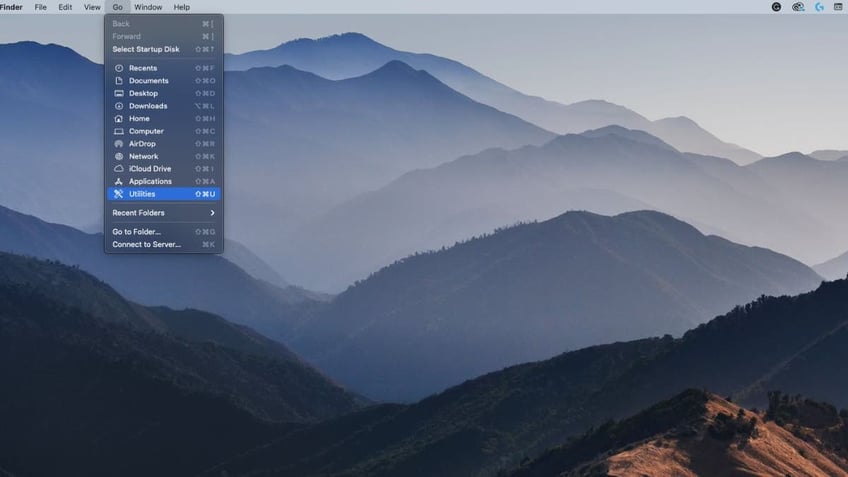
Encrypting your data on a Mac. (CyberGuy.com)
- Open Disk Utility
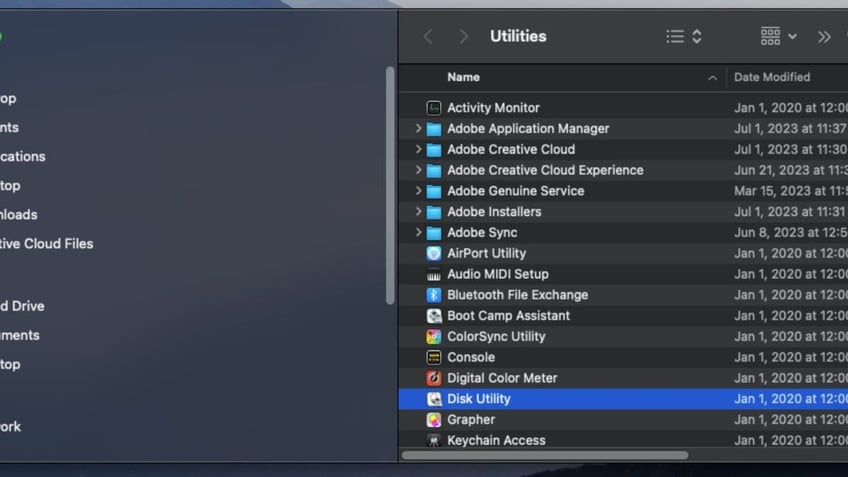
Here's where to go to encrypt your data. (CyberGuy.com)
- In the top left bar, go to File, then New Image right beneath it, and then Image from Folder
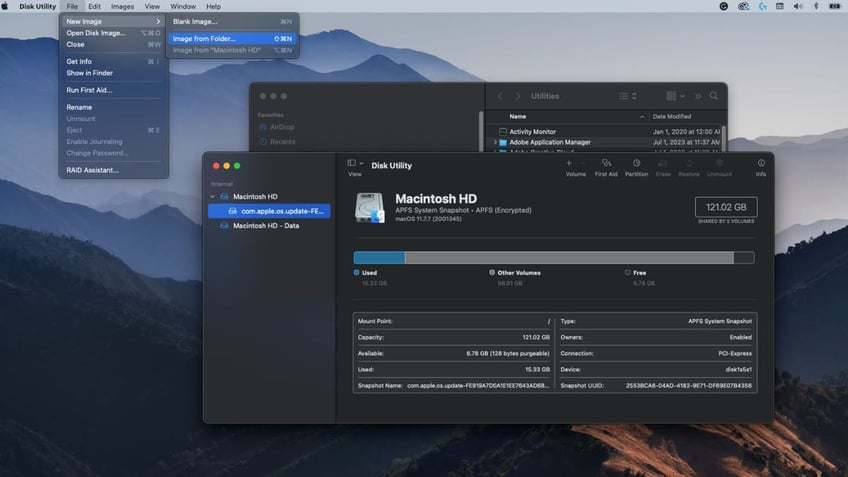
Select "Image from Folder" on your Mac. (CyberGuy.com)
- Find and select the folder you created
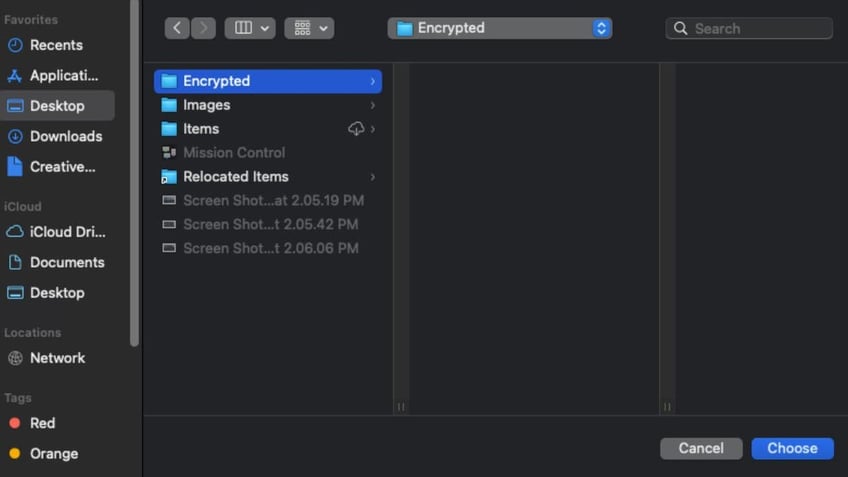
Look for the encryption folder you created. (CyberGuy.com)
- Click Choose
- Click on Encryption pulldown and choose 128-bit AES encryption
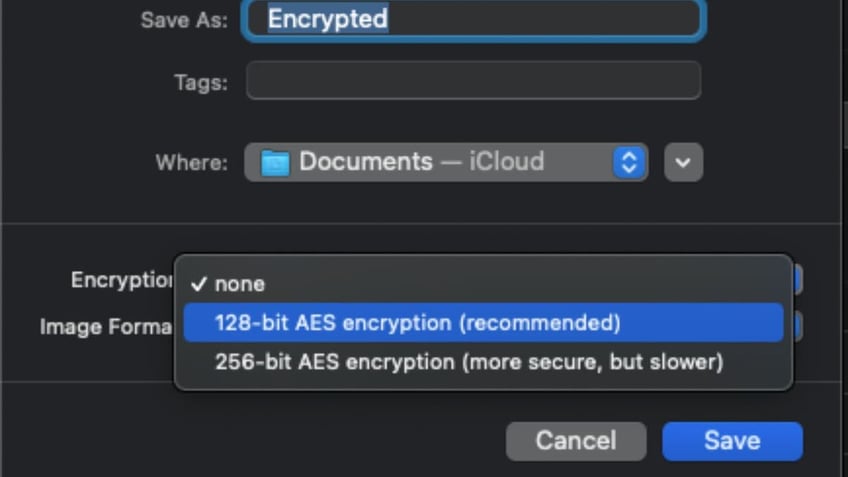
Here's the type of encryption to choose. (CyberGuy.com)
- Create a strong password and verify it by typing it in again. Then click choose.
- Select the Image Format pulldown
- If you want to be able to edit the file, select read/write; if you do not need to edit the file, select compressed
- Click Save
- Click Done
An encrypted copy of the file will be created in your preferred destination. However, the original, unencrypted folder will remain.
Now what should you do?

Look for this icon with a .dmg extension for your encrypted file. (CyberGuy.com)
CRIMINAL ENTERPRISE FLAUNTS AI IN CREEPY 'FRAUD-FOR-HIRE' COMMERCIAL MEANT FOR DARK WEB
The now-encrypted file will have the extension .dmg at the end of it. To test it, try double-clicking it to open.
When you attempt to open the file by double-clicking it, it will ask you for the password you just set to open the now encrypted file. After doing so, a "disk" with the same name will be created, which you can now find under the "Locations" area in your finder.
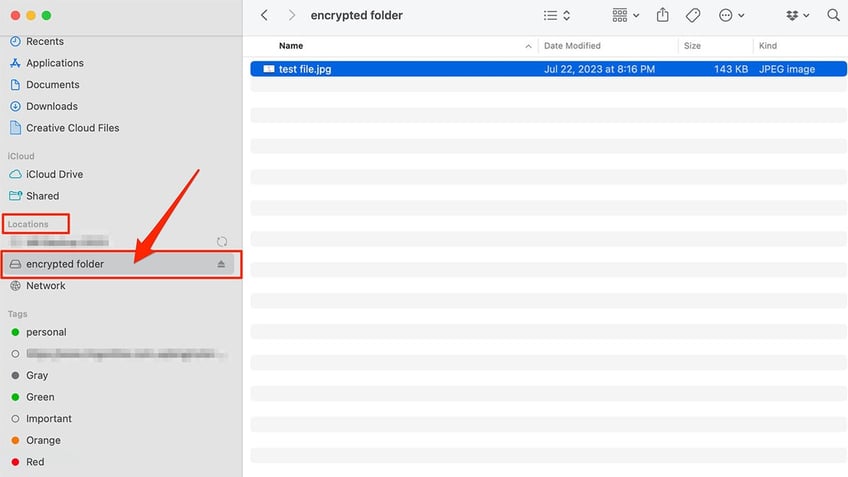
Here's where to test out your encrypted folder on a Mac. (CyberGuy.com)
After testing this out and opening it, for maximum security, it is recommended you move the original folder to the trash bin wherever you have it on your desktop. Then, click on the trash can, and select Empty Trash. Remember, after you do this, you won’t be able to retrieve the files. Be sure you have the password you just put into your password manager or written down in a good place.
Now, you will only have the encrypted file remaining.
ARE YOU PROTECTED? SEE THE 2023 BEST ANTIVIRUS PROTECTION WINNERS
What are the downsides to encryption?
Everything you encrypt becomes useless without the digital key. If you have many items encrypted in many different places, it can be hard to safely store or remember all of your different codes. In addition, if somehow the key is lost, forgotten, corrupted, or destroyed, there is no way to gain access to your information.
It is also important to realize that no security is completely impenetrable. While unlikely, there is a possibility that an outside source cracks your encryption key. The whole concept and doing it manually can be pretty complicated too.
Benefits of a password manager
One of the key ways to protect your data as you encrypt your documents is through the use of a password manager.
It will help you to create unique and difficult-to-crack passwords that a hacker could never guess. It also keeps track of all your passwords in one place so that you never have to remember them yourself.
The fewer passwords you remember, the less likely you will be to reuse them for your accounts.
Check out my best expert-reviewed password managers of 2023 here.
What to do so loved ones can access your files and data after death
Some providers may delete your files after a period of inactivity, while others may allow you to designate a beneficiary or a digital executor who can access your files after your death.
It is important to ensure your data or the data of your loved ones, is left in safe hands. There are a few different ways to ensure this.
If you encrypted files above, be sure to let your loved ones know that password otherwise they won’t be able to open your encrypted files.
To set up a legacy contact on a Mac, click here. To set up a legacy contact on a PC or Android, click here.
HOW TO BE REMEMBERED FOREVER ON FACEBOOK
What to do so loved ones can access your files on Google after death
Google lets the user set up an "Inactive account manager." This account will automatically contact the people you list after you have been inactive from your Google account for a chosen period of time. Here's how to set it up:
- Select this link
- Click Start
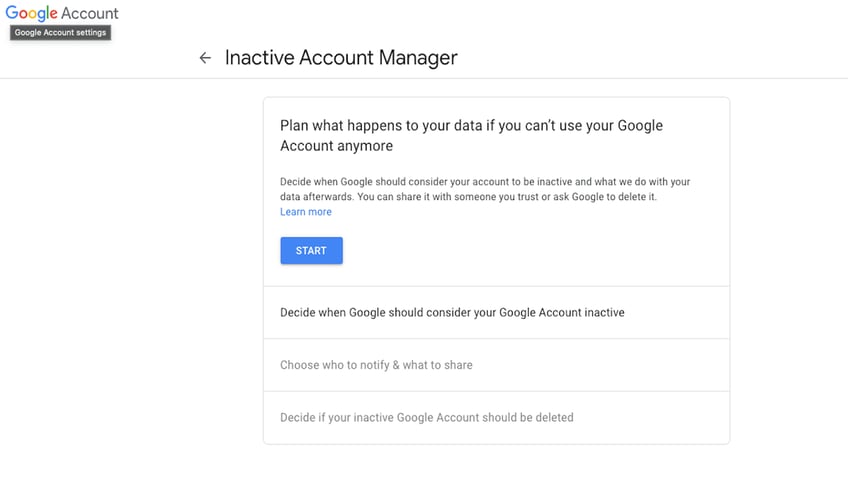
Encrypting your data on Google. (CyberGuy.com)
- Select the pencil icon to choose how long you want the period of inactivity to be
- Click Save
- Next, click ADD PHONE NUMBER and then type in your own phone number,
- If it sends you a verification code, enter in the given code and click VERIFY, then click NEXT on the bottom
- Then select ADD PERSON and add the email of who you want to be contacted and select NEXT
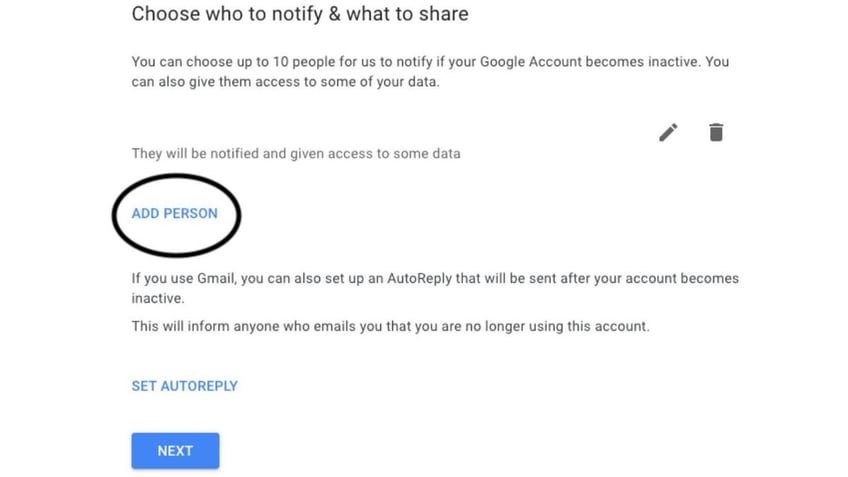
This is where you choose whom to notify on Google. (CyberGuy.com)
- Check the boxes of which data you want shared with the person, click NEXT, and add their phone number and click SAVE
- Repeat these steps for whoever else you want to have access
- Click NEXT at the bottom
- Select if you want your Google account to be deleted after death by ticking the switch, turning it blue
- Click REVIEW PLAN and then CONFIRM PLAN if you are satisfied
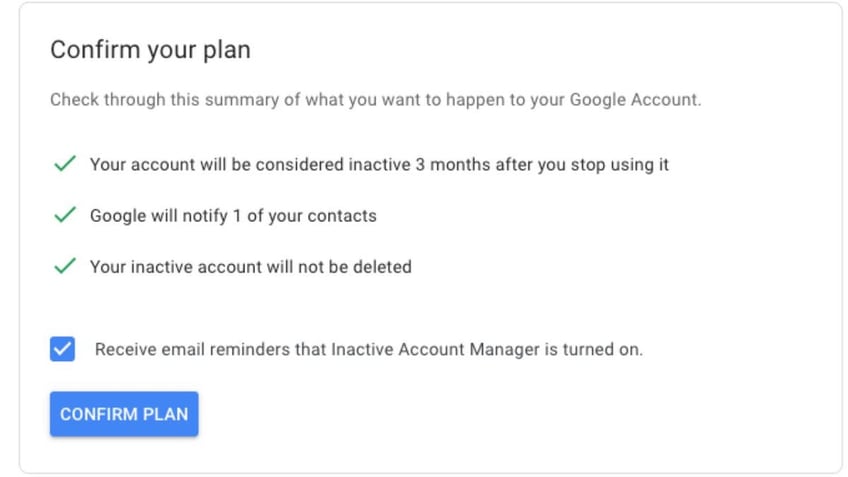
Then, confirm your plan to pass on your Google account. (CyberGuy.com)
Other methods to keep information and accounts safe after death
There are also alternative measures that can be taken to keep your information safe, even after death. Some password managers, like 1Password for example, have you create an Emergency Kit when you sign up, which includes all the information someone would need to log into your account. Print it out or download a copy to a USB drive and place it somewhere safe, like a lock box, where your loved ones can access it in the event of your death.
How do you feel about encrypting your documents before uploading them to the cloud? Are you prepared to ensure your data is accessible to close friends or family members after you pass away? Let us know by writing us at Cyberguy.com/Contact.
For more of my tech tips & security alerts, subscribe to my free CyberGuy Report Newsletter by heading to Cyberguy.com/Newsletter.
Copyright 2023 CyberGuy.com. All rights reserved.
Kurt "CyberGuy" Knutsson is an award-winning tech journalist who has a deep love of technology, gear and gadgets that make life better with his contributions for Fox News & FOX Business beginning mornings on "FOX & Friends." Got a tech question? Get Kurt’s CyberGuy Newsletter, share your voice, a story idea or comment at CyberGuy.com.
